ANZ uses Google tool to enforce security on containers and code - Finance - Cloud - Security - Software - Projects - iTnews

Implementing Binary Authorization using Cloud Build and GKE | Cloud Architecture Center | Google Cloud
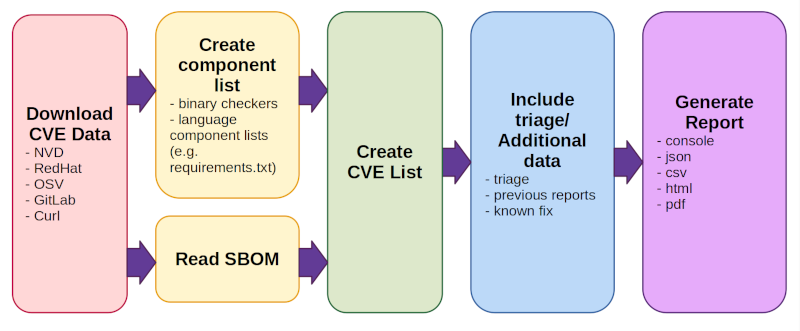
GitHub - intel/cve-bin-tool: The CVE Binary Tool helps you determine if your system includes known vulnerabilities. You can scan binaries for over 200 common, vulnerable components (openssl, libpng, libxml2, expat and others),

Vulnerability Scanner Showdown: AppDetectivePro 5.4.6 vs. AuditPro Enterprise 4.0 | ITPro Today: IT News, How-Tos, Trends, Case Studies, Career Tips, More



.jpg)